|
|
|

|
The term "security" is often seen in the press due to increased awareness of IT by society, the deterioration of the world order or the increase of the company scandals. However the term "security" is often used in differing contexts, such as information security, national security, or food or energy security. In other words, the term "security" is ambiguous thus security itself is difficult to treat as an object for systematic management or engineering practice. This is why makeshift security practices are implemented in a haphazard manner.
To change this situation and to understand security from a semantic viewpoint, we propose a new systematic approach for the fundamental meaning of the security. A dramatic paradigm shift regarding security will be possible with this approach[1,3].
|
|
| 1. The Fundamental Definition of Security |
|
To systematically handle security as an engineering object and to free security from haphazard implementations, we have abstracted the concept of security in all cases where the term "security" was used and define security as follows.
Security: The operation of the entity, as planned by the subject, undisturbed by any inhibitors.
In this definition, the entity refers to the organization, operation to the daily business of the organization, subject to the management or executive level of the organization and inhibitors to incidents which prevent the entity from operating according to plan.
For information security, unless the essential elements, "confidentiality," "integrity" and "availability" are fully satisfied, we are unable to operate not only the information systems but also the organization plan. Thus these three elements are emphasized as the essence of the information security and we can find many IT solutions in the market to satisfy these elements.
|
| 2. The Conditions for the Fundamental Definition of the Security |
|
The conditions to realize the fundamental definition of the security are:
- Identification of the operation and subject
- Existence of a clear operational plan
- Identification of the resource properties to execute the operational plan
- Identification of the inhibitors to the resource properties
- Risk management (risk control, risk finance and crisis management) to minimization the influence by the inhibitors
Using the fundamental definition and these conditions, all the cases where the term "security" is used can be explained. This sequence is the framework to implement security from the fundamental definition, which is applicable to all situations.
|
| 2.1. The Operation and the Subject |
|
When considering the security from a semantic viewpoint, the operation and the subject must be clarified and shared among the stakeholders. If this information is unclear, it becomes impossible to discuss security systematically because of divergence.
In the case of a company, the operation will be written in the by-laws of the organization and the subject must be an executive level member of the organization, generally the president or CEO. At home, the subject is generally the spouse or head of the household and operation is daily life.
If the entire organization like an enterprise is considered, the operation and the subject can be determined easily, in general. On the other hand, in the case of a division or an unit inside the enterprise, this information is often unclear.
|
| 2.2. The Operation Plan |
|
An operation plan written with a measurable quantitative property is preferable to a plan with immeasurable properties because deviations between the current status and plan are immediately apparent.
For a company, plans for each of the business units must be clearly written with measurable properties. For example, for the sales or manufacturing unit, a quota can be established. On the contrary, for units like public relations or general affairs, well established measurable properties are rare and these units must clarify their implicit knowledge, write up the plan as explicit knowledge and share it among the stakeholders even within their units, with measurable properties, if possible.
In the case of a home, domestic operation or "daily life" with a clear written plan is rare. Individual life may not suit such planning, but planning and sharing among family members is indispensable when thinking about domestic security systematically. This is the first step toward home security in a broad sense.
|
| 2.3. Resource Property |
|
After identifying the operation plan, all resource properties, both tangible and intangible, must be identified which are required in order to execute the operation plan.
In the case of an individual, health, housing, family members and income should be listed as typical resource properties. Including life, knowledge, memories and capabilities is not a problem. In the case of a manufacturing company, merchandise, market channels, customers, production facilities, employees, stock holders, cash flow should be the typical resource properties. These properties will depend on the type of industry.
Most properties will include a level as shown in Fig. 1. Therefore it is also important to think about the layering of the properties. An upper level property is composed of lower level properties, however if a lower level property is inhibited, the upper level property which depends on the lower level property will also be inhibited. In individuals, a hot water supply facility, essential household appliances such as a refrigerator will be the lower level properties and the living environment, which includes the lower properties, is one of the upper level properties.
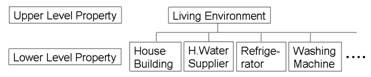
Fig.1 Example of the Property Level
The essential elements in information security, "confidentiality," "integrity" and "availability" correspond to the upper level properties of an organization. Before contemplating these elements, the operation plan of the company or the department must be clear. Although these three elements are the essential elements of information security, in implementation we often only discuss the lower level properties, i.e. the solutions, to achieve these elements. In spite of the importance of the preparation of these properties, defining the operation and fixing the operation plan of the organization are much more important than the preparation of the properties.
|
| 2.4. Inhibitor (Incident) |
|
After identifying the resource properties, incidents which can influence the resource properties must be considered.
If a house is an important property for an individual, physical incidents such as fires, hurricanes/typhoons and earthquakes and social incidents such as inflation adjusted rent payments or interest rate increases, like the subprime mortgage problems in the USA, would be examples of inhibitors. As an example of the compound inhibitors, housing seizures may occur due to income loss caused by health problems leading the inability to work.
In a factory of a manufacturing company, physical incidents would be similar to the case of the individual, and social incidents may include cease and desist orders by the authorities or courts.
In this case, multiple incidents occurring sequentially may inhibit the properties. Scandals or rumors about a company may damage the brand of the company leading to deterioration of sales, one of the most important properties of a company. This is an example of the linkage between incidents and properties.
When a problem occurs, the incident itself is recognized as the inhibitor due to its obviousness. But this obviousness frequently makes us lose sight of the essence of the problem. By thinking about security versus the incident, countermeasures are taken against the specific incident but leads to “makeshift” security treatments.
Consequently, we must think not only about the specific incident, but about security with regard to the operation and the operation plan. In the extreme case, the incidents will not be a problem if the operational plan is not disturbed. So why is it important to eliminate or minimize the influence of the inhibitors? This is because inhibitors influence the properties and inhibit the operation plan set by the subject.
|
| 2.5. Minimization of the Incident Influence |
|
After indentifying the inhibitors influencing the properties required to carry out the operation and the structure of the inhibitors, countermeasures against the each inhibitor must be found using risk management methodologies.
Generally, risk management methodologies are divided into two classifications in insurance. The first is risk control to decrease the probability of the risk itself, and the other is risk finance to prepare financial measures against the damage caused by the inhibitor.
Although crisis management is traditionally considered as a risk control measure, crisis management will be treated independently of risk control measures and defined as preventing the spread of secondary damage by preparing the initial response against incidents[2]. Namely, risk management consists of risk control, risk finance and crisis management as shown in Fig. 2.

Fig.2 Three Elements to Minimize the Influence of the Incident
In fact, these three risk management methodologies are the only protection against inhibitors. In other words, countermeasures against inhibitors need only be considered from a risk control, risk finance and crisis management perspective.
Risk management should be prioritized by the importance of the property itself and the probability and influence of the inhibitors.
|
| 3. Conclusions |
|
Without exception, we have to consider security to live in the contemporary world, whether as an individual or organization.
Therefore knowledge in a systematic approach towards security is significant. Living attitudes with this knowledge will bring large changes to society. It is time to say goodbye to the conventional stopgap security measures.
|
| 4. References |
|
[1] Yasufumi Amari: "A Metaconcept of the Security", Technical Report of IEICE, Vol.105, No.687 p.5-8 (2006) (in Japanese)
[2] Yasufumi Amari: "Basic Concept of the Security and Relationship between the Security and the Risk Management", Technical Report of IEICE, Vol.104, No.528 p.17-20 (2004) (in Japanese)
[3] Yasufumi Amari, et al: "New Knowledge of the Building Management", Chap. 6 ‘Theory of the Security’, Gijutsu Shoin (2007) (in Japanese)
|
| |
 |
|
|
|